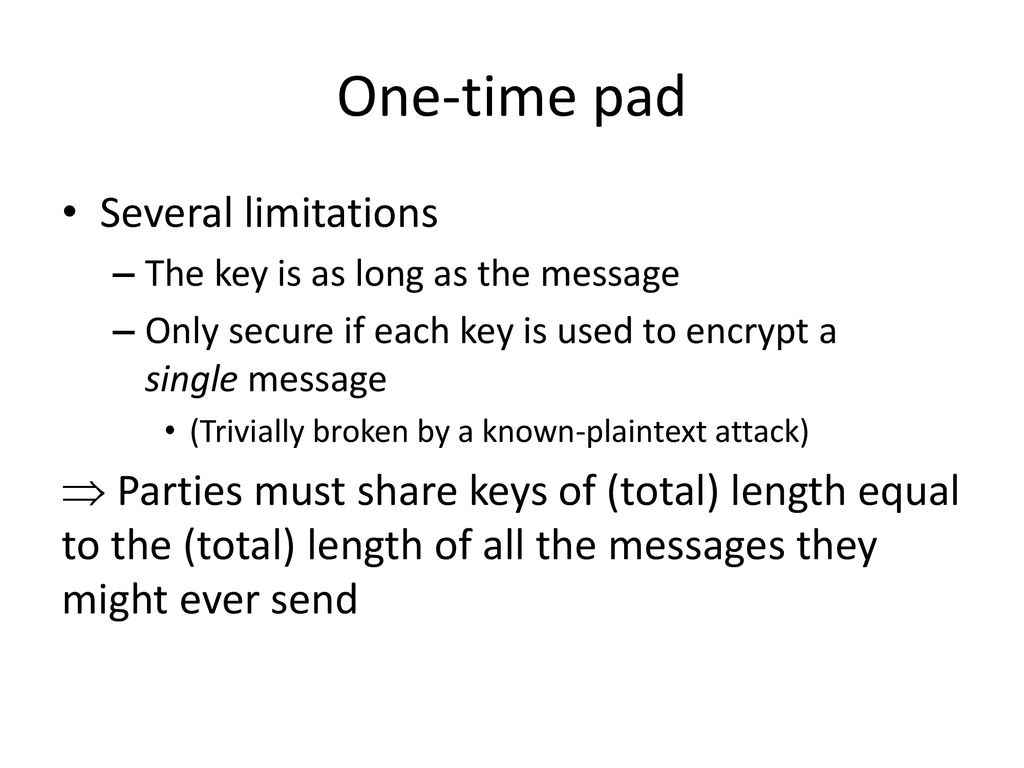
GitHub - Vishal-Kancharla/One-Time-Pad-Attack: Decrypting the one time pad messages when a single key is used many times.
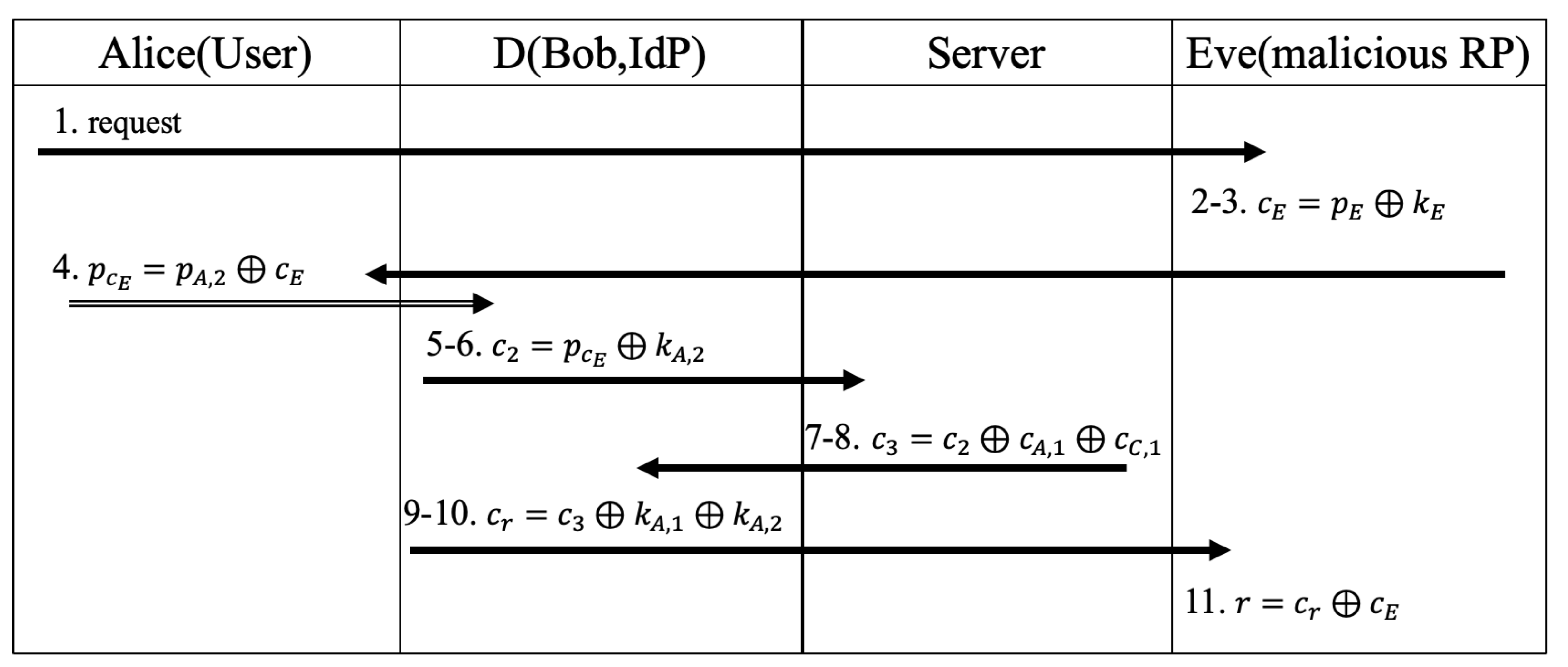
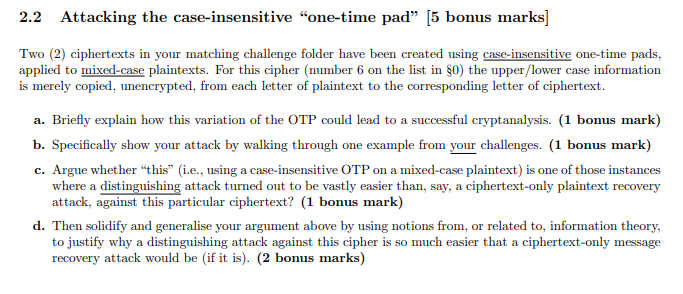
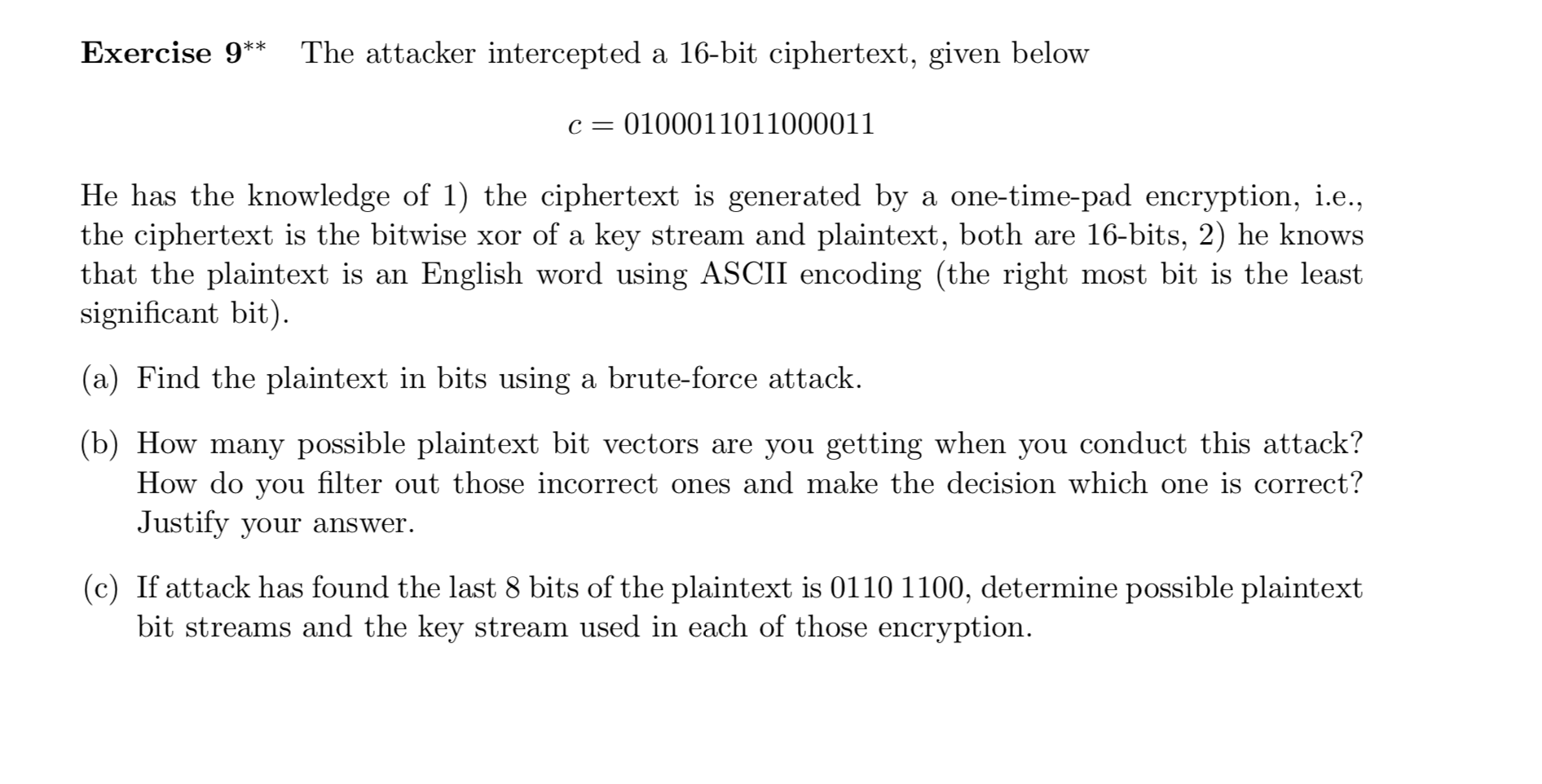
Cryptography | Free Full-Text | Security and Performance of Single Sign-on Based on One-Time Pad Algorithm
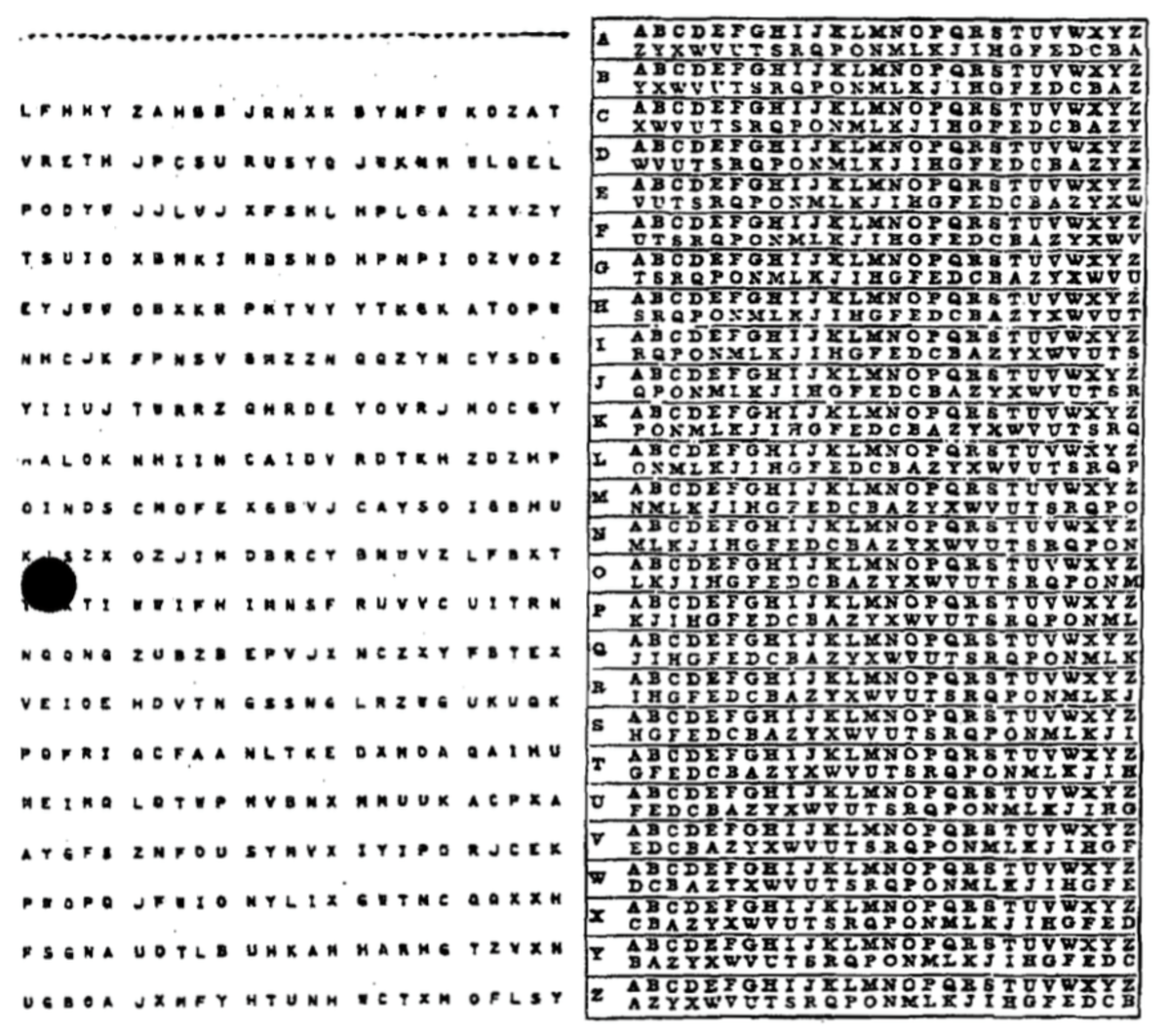
![PDF] An Enhanced Practical Difficulty of One-Time Pad Algorithm Resolving the Key Management and Distribution Problem | Semantic Scholar PDF] An Enhanced Practical Difficulty of One-Time Pad Algorithm Resolving the Key Management and Distribution Problem | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/5b2bd5573e4ae5daadea6141acb2d31e3d285ccb/6-TableII-1.png)
PDF] An Enhanced Practical Difficulty of One-Time Pad Algorithm Resolving the Key Management and Distribution Problem | Semantic Scholar
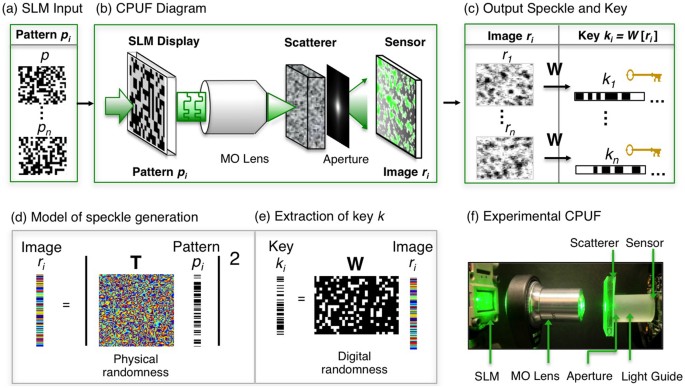
One-time-pad cryptography scheme based on a three-dimensional DNA self-assembly pyramid structure | PLOS ONE